At least once a year I try to publish my work process for a Capture The Flag (CTF) event. If you’re not familiar with CTFs, they’re a timed challenge of very difficult or obscure challenges to gain a “flag” to submit for points. Some enjoy these, some feel them a waste of time. At the …
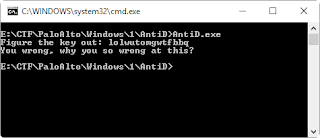
Running the Labyrenth: Unit 42 CTF